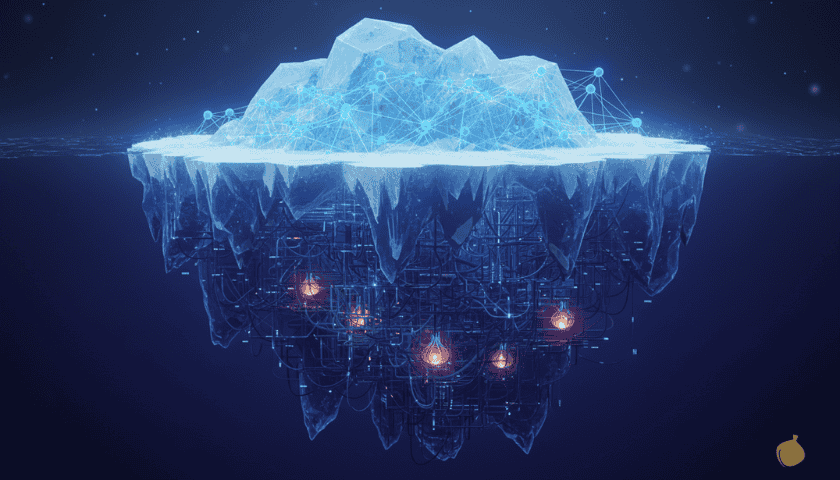
The hidden wiki 2026 is a website available on the dark web, an encrypted network designed to keep anonymity and privacy for its users. The site was created in 2011 with the intent of providing uncensored information from across the globe, and it has since grown into a vast repository of knowledge.
What does the Hidden Wiki contain
The hidden wiki is divided into many categories: politics, philosophy, science and technology, media and entertainment, security and privacy, and much more. It also provides access to various forums where users can discuss topics without being judged.
The hidden wiki is known for its ability to provide access to the dark web, which is otherwise difficult to navigate due to its encryption. The site offers a search engine, which can help users quickly find the information they are looking for. It also has a library of books, news sources, and links to other websites about the dark web.
Is Hidden Wiki Secure
Its developers take security and privacy on the hidden wiki very seriously. All user communication is encrypted, and all data stored on their servers is kept secure. In addition, the site does not store any personal data or logs about its users.
Overall, the hidden wiki 2026 has become a reliable source of information for those seeking to access the dark web without compromising their privacy. As long as users take steps to ensure their security and anonymity, they can browse safely without fear of being tracked or monitored. With its expanding library of resources, the hidden wiki 2026 is sure to remain a go-to destination for those seeking knowledge on the dark web.
How to access the Hidden Wiki
If you want to access the hidden wiki, use a secure browser such as Tor. It is important to note that the dark web can be dangerous, and it is best to exercise caution when browsing. Be sure to research the website before visiting, and never reveal your personal information or share any sensitive material while using it.
Uncensored Hidden Wiki – http://wiki47qqn6tey4id7xeqb6l7uj6jueacxlqtk3adshox3zdohvo35vad.onion/
Hidden Search Engines
- http://oniondxjxs2mzjkbz7ldlflenh6huksestjsisc3usxht3wqgk6a62yd.onion/ – OnionIndex Search Engine
- http://duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion/ – DuckDuckGo Search Engine
- http://3bbad7fauom4d6sgppalyqddsqbf5u5p56b5k5uk2zxsy3d6ey2jobad.onion/ – OnionLand Search
- http://tordexu73joywapk2txdr54jed4imqledpcvcuf75qsas2gwdgksvnyd.onion/ – tordex
- http://xmh57jrknzkhv6y3ls3ubitzfqnkrwxhopf5aygthi7d6rplyvk3noyd.onion/ – Torch
- http://juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/ – Ahmia
- http://metagerv65pwclop2rsfzg4jwowpavpwd6grhhlvdgsswvo6ii4akgyd.onion/ – MetaGer – German Search
Email Providers
- http://protonmailrmez3lotccipshtkleegetolb73fuirgj7r4o4vfu7ozyd.onion/ – ProtonMail
- http://tp7mtouwvggdlm73vimqkuq7727a4ebrv4vf4cnk6lfg4fatxa6p2ryd.onion/ – Alt Address
- http://secmail63sex4dfw6h2nsrbmfz2z6alwxe4e3adtkpd4pcvkhht4jdad.onion/ – secMail
- http://torbox36ijlcevujx7mjb4oiusvwgvmue7jfn2cvutwa6kl6to3uyqad.onion/ – TorBox
- http://eludemailxhnqzfmxehy3bk5guyhlxbunfyhkcksv4gvx6d3wcf6smad.onion/ – Elude.in
- http://j3bv7g27oramhbxxuv6gl3dcyfmf44qnvju3offdyrap7hurfprq74qd.onion/ – adunanza OnionMail Server
- http://mail2torjgmxgexntbrmhvgluavhj7ouul5yar6ylbvjkxwqf6ixkwyd.onion/– Mail2Tor
- http://hxuzjtocnzvv5g2rtg2bhwkcbupmk7rclb6lly3fo4tvqkk5oyrv3nid.onion/ – DNMX
- http://xdkriz6cn2avvcr2vks5lvvtmfojz2ohjzj4fhyuka55mvljeso2ztqd.onion/ – Cockmail
Forums / Social
- http://dreadytofatroptsdj6io7l3xptbet6onoyno2yv7jicoxknyazubrad.onion/ – dread
- http://germany2igel45jbmjdipfbzdswjcpjqzqozxt4l33452kzrrda2rbid.onion/ – Deutschland im Deep Web Forum
- http://answerszuvs3gg2l64e6hmnryudl5zgrmwm3vh65hzszdghblddvfiqd.onion/ – Hidden Answers
- http://suprbaydvdcaynfo4dgdzgxb4zuso7rftlil5yg5kqjefnw4wq4ulcad.onion/ – SuprBay: The PirateBay Forum
- http://rutordeepkpafpudl22pbbhzm4llbgncunvgcc66kax55sc4mp4kxcid.onion/ – Rutor
- http://enxx3byspwsdo446jujc52ucy2pf5urdbhqw3kbsfhlfjwmbpj5smdad.onion/ – Endchan
- http://c32zjeghcp5tj3kb72pltz56piei66drc63vkhn5yixiyk4cmerrjtid.onion/ – Raddle
- http://wbi67emmdx6i6rcr6nnk3hco3nrvdc2juxrbvomvt6nze5afjz6pgtad.onion/ – MadIRC
- http://thestock6nonb74owd6utzh4vld3xsf2n2fwxpwywjgq7maj47mvwmid.onion/ – The Stock Insiders
- http://facebookwkhpilnemxj7asaniu7vnjjbiltxjqhye3mhbshg7kx5tfyd.onion/ – Facebook
- http://notbumpz34bgbz4yfdigxvd6vzwtxc3zpt5imukgl6bvip2nikdmdaad.onion/ – Ableonion
- http://picochanwvqfa2xsrfzlul4x4aqtog2eljll5qnj5iagpbhx2vmfqnid.onion/ – picochan
- http://nanochanqzaytwlydykbg5nxkgyjxk3zsrctxuoxdmbx5jbh2ydyprid.onion/ – Nanochan
Hosting / Software Services
- http://fhostingineiwjg6cppciac2bemu42nwsupvvisihnczinok362qfrqd.onion/ – Freedom Hosting Reloaded
- http://spore64i5sofqlfz5gq2ju4msgzojjwifls7rok2cti624zyq3fcelad.onion/ – SporeStack
- http://hzwjmjimhr7bdmfv2doll4upibt5ojjmpo3pbp5ctwcg37n3hyk7qzid.onion/ – Ablative Hosting
- http://dds6qkxpwdeubwucdiaord2xgbbeyds25rbsgr73tbfpqpt4a6vjwsyd.onion/ – Whonix
- http://bcloudwenjxgcxjh6uheyt72a5isimzgg4kv5u74jb2s22y3hzpwh6id.onion/ – BlackCloud
- http://zerobinftagjpeeebbvyzjcqyjpmjvynj5qlexwyxe7l3vqejxnqv5qd.onion/ – ZeroBin
- http://keybase5wmilwokqirssclfnsqrjdsi7jdir5wy7y7iu3tanwmtp6oid.onion/ – Keybase
- http://oju4yn237c6hjh42qothvpreqecnqjhtvh4sgn3fqmsdvhu5d5tyspid.onion/ – Easy Image Upload
- http://uoxqi4lrfqztugili7zzgygibs4xstehf5hohtkpyqcoyryweypzkwid.onion/ – Image Hosting
- http://imghostoarpfmnf4pbktb47mxyphrqykjpxh6tny5wf7jmfa2sjdbryd.onion/ – imgHost
- http://lldan5gahapx5k7iafb3s4ikijc4ni7gx5iywdflkba5y2ezyg6sjgyd.onion/ – OnionShare
- http://iuploadi5zdzzx22mxgz7tgsj3z5av2szc76iymunuvvbfmqtmufplad.onion/ – iUpload
- http://spywaredrcdg5krvjnukp3vbdwiqcv3zwbrcg6qh27kiwecm4qyfphid.onion/ – Spyware Watchdog
- http://7sk2kov2xwx6cbc32phynrifegg6pklmzs7luwcggtzrnlsolxxuyfyd.onion/ – systemli.org
- http://cct5wy6mzgmft24xzw6zeaf55aaqmo6324gjlsghdhbiw5gdaaf4pkad.onion/ – Snopyta
Whistleblowing / News
- http://p53lf57qovyuvwsc6xnrppyply3vtqm7l6pcobkmyqsiofyeznfu5uqd.onion/ – ProPublica
- http://xp44cagis447k3lpb4wwhcqukix6cgqokbuys24vmxmbzmaq2gjvc2yd.onion/ – The Guardian | SecureDrop
- http://f3mryj3e2uw2zrv3zv6up6maqosgzn27frz7xodvpl7pkestoyigtkad.onion/ – AfriLEAKS
- http://27m3p2uv7igmj6kvd4ql3cct5h3sdwrsajovkkndeufumzyfhlfev4qd.onion/ – The Intercept
Hacking
- http://relateoak2hkvdty6ldp7x67hys7pzaeax3hwhidbqkjzva3223jpxqd.onion/ – RelateList
- http://blackhost7pws76u6vohksdahnm6adf7riukgcmahrwt43wv2drvyxid.onion/ – Hacker Game
Others
- http://lpiyu33yusoalp5kh3f4hak2so2sjjvjw5ykyvu2dulzosgvuffq6sad.onion/ – Tech Learning Collective
- http://kx5thpx2olielkihfyo4jgjqfb7zx7wxr3sd4xzt26ochei4m6f7tayd.onion/ – Imperial Library of Trantor
- http://t3qi4hdmvqo752lhyglhyb5ysoutggsdocmkxhuojfn62ntpcyydwmqd.onion/ – TorStatus
- http://kaizushih5iec2mxohpvbt5uaapqdnbluaasa2cmsrrjtwrbx46cnaid.onion/ – KaizuShi
- http://afajj7x4zfl2d3fc2u7uzxp4iwf4r2kucr5on24xk2hwrssoj7yivhid.onion/ – Simple Bookmarks
- http://7fc532c5lvbky6lxlt3gxnbj67gqmpzym2rowtekllgypyprbjxfiiad.onion/ – My Onion Bookmarks
- http://stormwayszuh4juycoy4kwoww5gvcu2c4tdtpkup667pdwe4qenzwayd.onion/ – cryptostorm
- http://nehdddktmhvqklsnkjqcbpmb63htee2iznpcbs5tgzctipxykpj6yrid.onion/ – LocalMonero
- http://cgjzkysxa4ru5rhrtr6rafckhexbisbtxwg2fg743cjumioysmirhdad.onion/ – Coarse Enigma
- http://njallalafimoej5i4eg7vlnqjvmb6zhdh27qxcatdn647jtwwwui3nad.onion/ – Njalla
- http://vvedndyt433kopnhv6vejxnut54y5752vpxshjaqmj7ftwiu6quiv2ad.onion/ – PsychonauticsWIKI
- http://2jopbxfi2mrw6pfpmufm7smacrgniglr7a4raaila3kwlhlumflxfxad.onion/ – AgoraDesk
- http://ciadotgov4sjwlzihbbgxnqg3xiyrg7so2r2o3lt5wz5ypk4sxyjstad.onion/ – The CIA
- http://digdeep4orxw6psc33yxa2dgmuycj74zi6334xhxjlgppw6odvkzkiad.onion/ – Dig Deeper
- http://ncidetfs7banpz2d7vpndev5somwoki5vwdpfty2k7javniujekit6ad.onion/ – NCIDE Task Force
- http://tcecdnp2fhyxlcrjoyc2eimdjosr65hweut6y7r2u6b5y75yuvbkvfyd.onion/ – National Police of the Netherlands
- http://elfqv3zjfegus3bgg5d7pv62eqght4h6sl6yjjhe7kjpi2s56bzgk2yd.onion/ – Fake ID Generator
- http://elfqv3zjfegus3bgg5d7pv62eqght4h6sl6yjjhe7kjpi2s56bzgk2yd.onion/binfo_check_anonymity.php – Check your anonymity online
- http://bvten5svsltfpxrxl72ukqxixwo2m5ek5svmcxgrmkta4tbmiemuibid.onion/ – Beneath VT
- http://potatoynwcg34xyodol6p6hvi5e4xelxdeowsl5t2daxywepub32y7yd.onion/ – Go Beyond
- http://anonyradixhkgh5myfrkarggfnmdzzhhcgoy2v66uf7sml27to5n2tid.onion/ – Deep Web Radio
Are VPNs necessary to access the Hidden wiki
VPNs are becoming increasingly popular as an online privacy tool, but they can also be used to access the dark web. The dark web is a hidden website network that uses anonymous communication protocols to protect users from identification and surveillance.
It can be accessed through special browsers, such as Tor or I2P, which allow you to browse the internet without revealing your proper IP address. However, using a VPN in addition to these browsers can provide an extra layer of security and privacy.
How does an VPN work
By connecting to a VPN server before accessing the dark web, your internet traffic will be encrypted and routed through a secure tunnel that is difficult for attackers to breach.
This helps protect your data from cyber criminals trying to access your information. Additionally, a VPN can help hide your valid IP address from websites on the dark web, making it even more difficult for hackers to track you down.
With a reliable VPN service, users can securely and anonymously access the dark web while preserving their privacy and security.
By taking the necessary steps to protect your privacy and browsing securely, you can enjoy the anonymity and uncensored knowledge provided by the Hidden Wiki 2026 without compromising your safety.
The Deep Web
The Deep Web is a kind of Internet that is not indexed by search engines. The domain of the deep Web is the dark Web, which is present inside a layered proxy network called dark Net. Of these darknets, Tor is awesomely large. It is a web that is not accessible by search engines, such as personal government data, bank data, or cloud data. This data is sensitive and private and therefore is stored out of reach. Used to deliver access to a specific group. In the deep Web, users intentionally bury data.
Surface web
The pages in the search engine index are part of the surface web. It includes traditional web pages, blog posts, and forums.
Choosing which videos to watch on YouTube’s homepage is a widescreen process. Anyone can reproduce it. The web address of the video and the page it is on is almost always the same for everyone.
Access to the surface web requires an internet connection and a web browser. Depending on your location and device, there may be slight differences in page layout. However, anyone in Japan, the United States, or Sweden (not necessarily China) can access the video directly.
And once the web crawler visits, people can find it by typing the words related to the search engine.
Understanding of the Deep Web
In order to properly comprehend how the Deep Web operates, you first need to understand some basic things about how the Internet works in general, especially with search engines.

Crawling
Crawling is the search engine’s process of finding new content and websites on the Internet. Search engines do this by automated bots called crawlers. The crawler starts from a website that the search engine already knows about, visits all the links on that website, and then does the same thing on the next site.
It is the main way search engines recognize certain websites and webpages and, generally, how sites such as Google add webpages to the index. This allows users to find the site through its search engine.
Indexing
The next thing the search engine does after crawling is indexing. In general, it’s a process by which a search provider’s crawler bot saves and classifies web pages and sites it finds, making it easier for users to find relevant results when they search for something.
The sites stored in the index are ranked based on various factors, and how high they are displayed on the search result page is determined.
Delivery
Like Google, the final stage of the search engine process is Serving. To receive a retrieval query from a user, to find the most relevant result from an index, and to provide a Web page of the result to the user.
Deep Web includes
The Deep Web, also comprehended as the Invisible or Hidden Web, is a considerable part of the Internet. You won’t be able to find these pages in search results from search engines, but you may visit them daily.
Deep Web directs to any page on the Internet that is not indexed by the search engine as described above. The Deep Web is the first level under the visible “surface” of the Web, much larger than the surface web, and is estimated to account for 96% to 99% of the Internet overall.
What is important here is that the lack of this type of content on the surface does not mean that it is malicious or not malicious. This type of content is often not indexed because it contains pages hidden to protect consumer privacy, such as pages requiring login information.
Examples of content on the Deep Web:
Paid content: Paid content such as news articles and subscription content that requires login verification is considered part of the Deep Web. For example, if you pay to access subscription content at a content creator’s fan club, you are using paid content.
A database that contains protected files that are not connected to other areas of the Internet. It can be a public or private file, such as a government agency or private educational institution.
Intranets, such as educational institutions, companies, and governments, are used to exchange and organize internal information. Some of this information is confidential and is not intended to be disseminated to the general public. Intranets usually demand a login and are part of the deep Web.
Secure storage platforms such as Dropbox and Google Drive also need you to log in to upload and download files and photos. There are also proprietary data storage solutions used by companies that frequently deal with sensitive data, such as law firms, financial institutions, and healthcare organizations. For example, a hospital or clinic patient portal can access a person’s medical records.
Login Pages: All web pages requiring a login are part of the deep Web. However, the content of the Deep Web can fall outside of these categories. Pages that cannot be indexed are technically considered part of the deep Web. You do not need to log in or contain sensitive data. Website creators and administrators can mark pages as non-indexable if necessary. Note that a single organization’s Web site can contain surface and deep Web elements. For example, consider a university website. Most schools have a comprehensive website that provides information about school history, campus location, number of students, available programs, extracurricular activities, and more.
Example:
However, many schools have an intranet (sometimes linked from the university’s main page) that only students and staff can access. For example, students can sign up for classes or access school email from this intranet. It is confidential and requires a unique login, so you don’t need to publish it to the public in search engines.
Rather, to protect your privacy, it is better to avoid seeing such a page easily. It helps protect your data. This example shows that the Deep Web does not have to be scary, rogue or illegal. Having a legitimate and useful end. You don’t have to be terrified of the Deep Web. In addition, it is important to distinguish between the deep and the dark Web – we will explain this in the next section.
How to access the Deep Web Hidden Wiki?
Deep Web information is not indexed by the normal search engines but is often accessible.
Access to content on the Deep Web is relatively secure and is something that most Internet users do all the time. Logging in to Gmail, LinkedIn, or Wall Street Journal is just one example of accessing data on a deep website. User accounts on the Deep Web contain much personal information that criminals can find valuable.
The deep Web, comprising the dark Web, will never reach into your hands. Spam and phishing attacks may come from a dark web marketplace, but users must download infected malware from that marketplace to release it. The attack will not come from the dark website itself.
The Dark Web is intentionally hidden, and access requires certain technologies such as Tor browsers and Invisible Internet Project (I2P) networks. Both tools have legitimate uses. Tor protects I.P. when browsing websites, and I2P is a proxy network that helps journalists report from dangerous areas.
Method for Accessing Deep Web Content
The Internet is considered to be the deep Web for some but only for some. In China, for example, the Internet is severely restricted, so most of the Internet that people in most other countries have free access to is enclosed in a wall. Localized search engines do not provide such links.
News sites and streaming services often offer content that varies from region to region. Or it may completely block access.
Fortunately, you don’t have access to all of this content. With a VPN service or proxy, you can make yourself appear as if you are in the area you need. It is disgusting, but many people outside the U.S. utilize such tools to access American content on Netflix and other movie sites.
Deep Net Website
Websites only on the Deep Net have other access, so there is a level of privacy on the website host that is impossible on the normal Internet. If your website is only accessible through Deep Net, tracking the server’s physical location is much harder than with a regular website.
Deep Net provides this level of privacy to website hosts because the .onion address used to access the website obfuscates the actual I.P. address of the server. It makes it impossible to track the physical server under normal circumstances.
The anonymity of the website host distinguishes the deep Web from the surface web, allowing people to host web content (legal or illegal) while being hidden from authorities.
Tor
Further down to the bottom of this ocean is the Tor network, the darkest part of the Web. It consists of a series of personal websites whose addresses end in. onion and requires special software to connect. This software is known as Tor. Many people use this software to access the Internet anonymously. This is because the software encrypts all content that passes through it.
Tor is a virtual tunnel network that bounces and protects user communications within a huge network maintained by volunteers worldwide. It was originally designed to protect government communications as a routing project for the U.S. Naval Research Institute.
Is it illegal to use Tor?
On the software side, using Tor and other anonymized browsers is not strictly illegal. In fact, these “dark web” browsers aren’t just tied to this part of the Internet. Today, many users use Tor to personally browse the public Internet and deeper territories of the Web.
The privacy presented by the Tor browser is vital in the current digital age. Companies and government agencies are also currently participating in unauthorized surveillance of online activities. Some people, even government agencies and Internet service providers (ISPs), may want to avoid knowing what they see online, while others have small choices. People in countries with difficult access and user laws usually only have access to public sites if they use Tor clients or virtual private networks (VPNs).
However, it is possible to carry out illegal activities within Tor that may bring you into sin, regardless of the legality of the browser. You can easily use Tor to try to pirate copyrighted content from the Deep Web, to share illegal pornography, or to engage in cyberterrorism. Even if you use a legitimate browser, your actions won’t fall on the right side of the law.
The cyber threat in the Deep Web
Content on the Deep Web is hidden from search engines, making it harder to find and find that content on the surface web indexed in Google.
Taking advantage of this, digital threats are using the deep Web to cover up malicious and rogue infrastructure that can be used for fraud and cyberattacks. Malicious or impersonated domains created by digital threats are commonly hidden from Google in the deep Web and used to carry out scams and steal access certificates from victims.
The Deep Web also includes a private forum where hackers exchange tools and information for carrying out attacks against corporate targets.
Why should you avoid the Deep Web?
Many areas of the Deep Web are safe. It contains a database of companies and the personal information of billions of consumers. You access it regularly. However, you can be in danger once you start exploring the Deep Web.
Most of the Deep Web is encrypted to stop hackers, so in most cases, you won’t have access to the kind of information you care about.
If there is anything in the Deep Web, it is for a reason. It’s something you only want to do yourself sometimes. It includes more bad stuff like a snuff film, child pornography, hired hitmen, hackers, etc. The FBI may alert you if you come across something like this. If more is needed, there are also a lot of scams. You can use tips and tricks to get started with hacking or a handy hacking tool. It then accesses your computer and steals information. In most cases, it’s not worth peeking into the deep or dark Web.
Difference between the Deep Web and the traditional Internet
By explaining how the traditional Internet works, you can understand how the Deep Web differs. The Deep Web is a “hidden” site, no matter where you look because it is not visible from crawler bots or search engine indexes.
In other words, if you like to access a site on the Deep Net, you must understand the specific web address beforehand or use a search engine dedicated to the Deep Net. Conventional search engines such as Google could be more useful.
Dark Web vs Deep Web: What’s the distinction?
The difference b/w the dark and the deep Web is that the deep Website directs to sites and web pages that are not accepted by search engines, such as login pages and payment portals. On the other hand, the Dark Web includes of Dark Net, an online network accessible only by specialized software and technology.
The Deep Web consists of all the content that exists behind paywalls, authentication forms, logins, and passwords. Much of the content that ordinary people access on the Internet, such as mail, internet banking accounts, social media secret accounts, and subscription services, is included in the Deep Web. It would be a problem if my email history was published on the surface web and anyone could search it.
Ransomware and ID Theft on the Dark Web
Although it is not necessarily an investment in Bitcoin, many organisations are forced to become familiar with Bitcoin as soon as they are hit by ransomware.
Ransomware is a kind of malicious software operated by hackers that locks a particular file or entire system until the victim makes a payment. For the reasons mentioned above, Bitcoin is often a necessary payment method. These attacks are often time-consuming and force organizations and individuals to pay as soon as possible. In such cases, the dark Web has a huge impact on facilitating cyberattacks.
It’s not just the risk of a ransomware attack; it’s also the chance of being the victim of a breach of personal information as a result of unknowingly posting information on the dark Web.
The dark Web has an image of credit and debit card numbers being stolen, but many people are surprised to learn that the most valuable data in the dark Web is the leaked medical information. The Dark Web sells all kinds of personal information, many of which come from well-known data breaches. However, not only the stolen credit card number but also the personal information available on the Dark Web can be a victim of identity theft.
How to protect the end user from the exploitation of the Deep Web?
Whether you are a user of the deep Web or not, whether you are a business or a parent, we want to take precautions to protect your information and personal life from the deep Web.
To prevent personal information from being misused, it is important to monitor the leakage of personal information. All types of personal information may be distributed online for a profit.
Passwords, addresses, bank account numbers, social security numbers, etc., are always distributed on the dark Web. You may already know that malicious actors can use these to damage your reputation, commit financial theft, and break into your other online accounts. Also, personal information leakage can damage your reputation through social fraud.
Anti-malware and virus protection is equally important to ensure that malicious parties do not exploit them. The deep Web continues to receive information from users infected with malware. Attackers can use tools like keyloggers to collect data and break into your system anywhere on the Web. Endpoint security programs such as Kaspersky Security Cloud are comprehensive, covering both identity monitoring and antivirus protection.
Use the Deep Web Tool to find out information.
As you can see, the thing behind paid walls, usernames and passwords, or CAPTCHA, is technically deep Web. You may not know that many online tools on the deep Web display live content. Here are some examples:
You can watch flight delays live in the United States at FAA’s Air Traffic Control System Command Center. With Melissa, you can check the names and addresses of people all over the world.
The U.S. Department of Transportation offers an excellent tool to search for safety issues and recalls recorded for each vehicle. Enter the vehicle body number to find out if your vehicle is safe.
Project Gutenberg has over 60,000 free eBooks that can be read on eBook readers, computers and tablets.
Business of the Dark Web
Research thinks readers like to read about crime and the dark side of the hidden Web, so let’s give an example of a website related to illegal activities.
In this way, the anonymity secured by the Tor network represents an attractive spot for the criminal industry. It creates ideal conditions for securing businesses that need help tracking between sellers and buyers of any goods they trade.
On the Deep Web, it is virtually possible to get all kinds of illegal products and services, from drugs to weapons, and recently websites that offer hacking tools, services and exploits have been very successful. Prices range very much from hundreds to thousands of dollars in the case of zero-day attacks and complex malware.
Final Thoughts
The Deep Web is a secret part of the Internet world. It may contain websites or web pages that are prohibited from indexing by search engines or newly created websites that still need to be within the scope of search engines.
The dark Web shows no sign of losing its appeal as the desire for privacy grows. In less than 20 years, the network has been transformed from a separate project to support anonymous communications to a large, unregulated network. You should now be able to better understand the vast amount of web content that is unknown to search engines and the general public. You’ll also find out how to get to the Deep Web and why the Deep Web exists in the first place. We also looked at the differences between the dark and deep Web and how the deep Web is increasing its anonymity to the next level.